User secrets are personal to you - your API keys, tokens, and credentials available in every environment you create. They’re ideal for personal access tokens that shouldn’t be shared with the team. User secrets have the highest precedence. They override project and organization secrets with the same name, letting you customize without affecting teammates.Documentation Index
Fetch the complete documentation index at: https://ona.com/docs/llms.txt
Use this file to discover all available pages before exploring further.
When to use user secrets
Use user secrets when the credential belongs to an individual rather than to the team. Common examples:- your personal GitHub or GitLab token
- your personal Linear or Notion token
- credentials for tools only you should use
- temporary tokens you are testing before standardizing them at project or organization scope
Manage user secrets
Navigate to Settings → My Account → Secrets.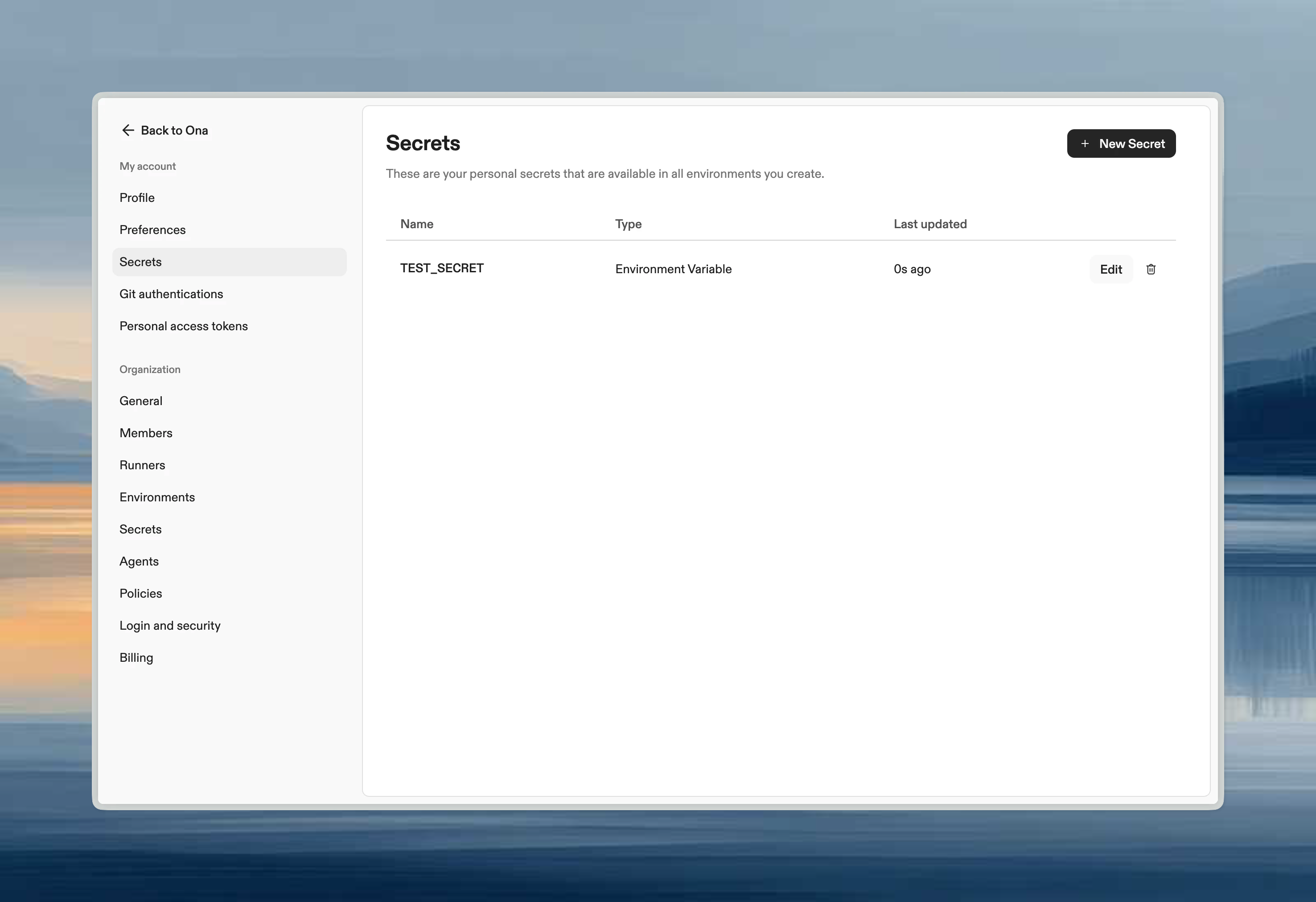
Common user secrets
| Secret | Purpose |
|---|---|
LINEAR_API_KEY | Personal Linear access |
GITHUB_TOKEN | Personal GitHub token |
NPM_TOKEN | Private npm registry access |
When to use user vs project secrets
- User secrets: Personal tokens, credentials you don’t want to share
- Project secrets: Shared team credentials, service accounts, project-specific config
How user secrets interact with other scopes
If the same secret name exists at multiple levels:- user secret wins
- project secret is used next
- organization secret is the fallback